Technology has made it much simpler for investigators to detect crimes. The professionals can use collected data to analyze cybercrime.
This practice is popularly known as computer forensic investigating. So, what is a day in the life of computer forensics? What roles does this profession cover?
I will share with you my personal experience working as a computer forensics investigator. I hope my story can give you more insights into this profession.
A Day In The Life Of A Computer Forensics Investigator
There are no two same days in the work life of computer forensics. The duty and tasks I have to do vary in cases. The sections below will give you a brief overview.
Job Overview
Forensic science is a medical domain that has existed since the 18th century. It involves scientific practices that help experts solve a crime.
However, the term computer forensics is different from the traditional cases. It deals with crimes like hacking and attacking online systems.
They typically include factors like:
- Digital data
- Trace evidence
- Digital DNA
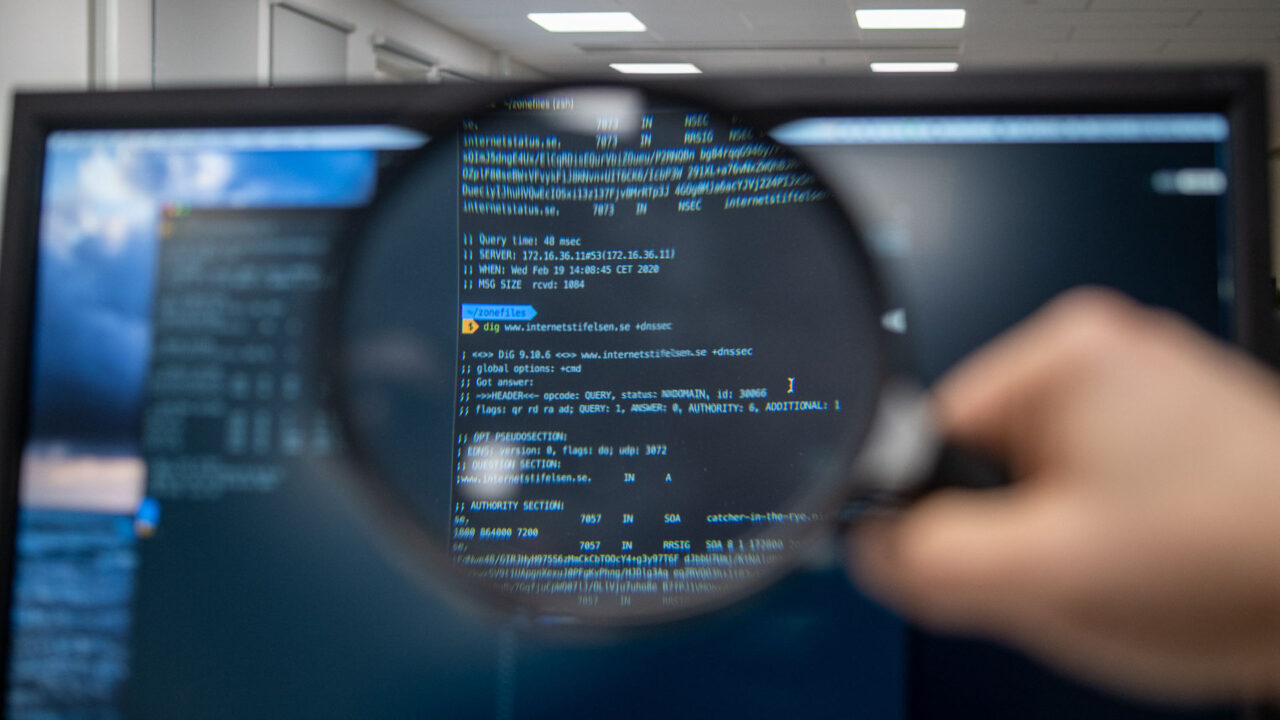
The experts will use tools to collect data from a cybercrime incident. They will use special tools to look for the marks of the digital left on the crime scenes.
Then, the forensics investigator will use software to analyze these data. It will help them look for traces of evidence and identify the culprit.
It’s also the main goal of my profession. I use modern technology to analyze the data and assist the investigators.
Also, I can identify the causes of the online attacks and the tools hackers used to attack the systems. Therefore, online companies will need forensic investigators to find out who attacked their systems.
Main Duties
Most forensic investigators typically work for law agencies and government bodies. They can also work as an independent contractor. In my case, I work for a law agency firm that connects with many online businesses.
When a system gets hacked, the owner will contact my firm. Then, the investigating team will research the case and help identify the culprit.
Besides attacks, I can help develop evidence for fighting against online fraud. Here is a typical example of my daily work and schedule.
Work Hours
Like the other jobs, I follow an 8-to-5 working schedule at my law firm. I spend the first 15 minutes at work checking my mail and the company’s network.
So, I can keep track of the latest changes at work and tasks assigned. Then, I will have a short discussion with the team manager to keep up with today’s schedule.
After the discussion, I will sit at my desk at 9:00 AM and prepare for the tasks. I have a break at 12:00 AM for lunch and continue the afternoon work at 1:00 PM.
My work day ends at 5:00 PM when I finalize the tasks before going home. So, what typically happens in a day at my workplace? The sections below will show you more details.
Testing And Collecting Data
Typically, my role is to collect data on the customers’ network and perform a variety of security checks.
I will monitor the network and check if there are any security loops. My work helps increase the system’s stability and protect it from cyber-attacks.
I also spend a lot of time collaborating with the other team members. The team will discuss and find the best methods for testing data on a network.
Most of my daily work revolves around data collecting and testing. Yet, the duties can get a lot more intense when a crime happens.
Dealing With Cyber Crimes
Normally, customers will contact our company if their systems get hacked. In such cases, their valuable data and digital assets may have been stolen.
In such situations, my team will take charge of investigating the incident. I will review the incident based on the customers’ reports first. Then, I will use special tools to collect data from the event.
The analyzing tool will process the data and look for the marks of a culprit. For example, I will analyze the important files of the system. Normally, I can identify if someone has stolen or altered the information.
I also analyze the network’s memory and history of operation. If there are any suspicious traits detected, I will report them back to the team manager.
Then, the team will track the evidence and find out the trace of the culprit.

Who Works As A Computer Forensics Investigator?
Forensic is a high-level position. The investigators are typically experts who have built a deep foundation in networking and IT security. They also possess high skills and knowledge in computer science.
Investigators must possess deep experience in dealing with online crimes. They also deliver a good performance and solve many cases to advance to this level.
Is A Computer Forensics Investigator The Right Profession For You?
This field features a very competitive wage in the IT industry. ComputerCareers reported that computer forensics investigators earn a high average salary.
Despite the high income, this career path is very challenging, even for IT professionals. There’s no expert that starts their career as a forensic investigator.
They have to start from a low position and accumulate experience to reach this role. Also, you must possess high technical skills.
If you possess the mentioned qualifications, don’t hesitate to pursue this career path. It will bring you a competitive wage and high recognition in the field.

Final Thoughts
A competent investigator can track criminals using the most subtle evidence. So, this profession holds a critical role in protecting assets from online attacks.
My story only covered a tiny fraction of what computer forensic investigators do. I hope you have understood about this career path after reading the post.
Thank you for reading!
